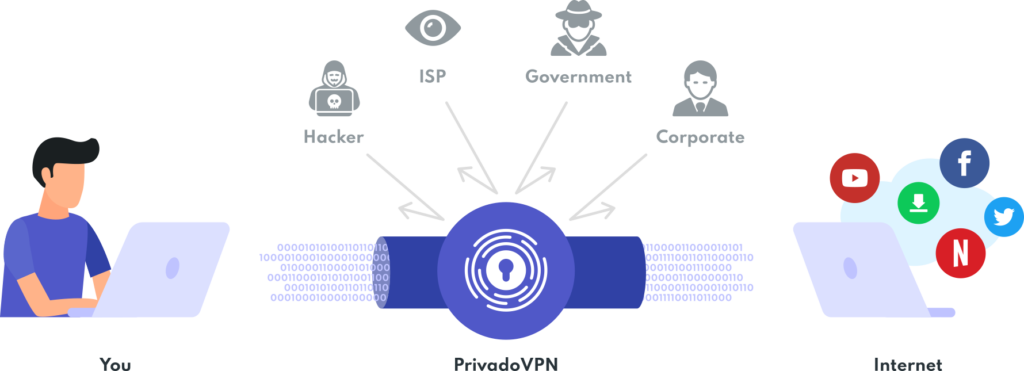
So, you’ve been convinced that a virtual private network is crucial to your Internet safety. You understand that they are indispensable tools that keep a wide range of threats at bay. But now that you have one, what VPN protocol should you be using?
What is a VPN Protocol?
A VPN encryption protocol is a rule that your virtual private network uses to scramble your data before it gets sent over the Internet, protect it in transit, and put it back in the right order when it reaches its destination. They regulate how your client (like the PrivadoVPN app) talks to your server (like any of the servers we have in 46+ countries) and determine the best way to get your data from one place to another.
There are several VPN protocols because there are a lot of ways to go about these complex negotiations. The two primary factors that you should keep in mind are speed and security. The more secure a protocol is, the slower it will be because it requires more time to protect your data. The faster a protocol is, the less safe it will offer you because the greater concern is getting the data from you to someplace and back again.
What To Look For
Even though proprietary solutions from Microsoft and Cisco helped pioneer VPN development, there has been a significant drop in confidence for many of these types of protocols. Open-source solutions have instead gained significant popularity since the early 2000s. Attempts to outlaw end-to-end encryption in regard to law enforcement have encouraged people to rely on open-source solutions that aren’t as closely tied to the government.
Furthermore, it’s important to have an easy set-up, since this isn’t an area you want to have doubts about it working properly. Many protocols are not built into your devices. Even when they are, you sometimes need a little tech-savvy to deal with system-embedded firewall restrictions and updates. Thankfully many of the provider solutions do offer easy, client-facing automated installations (including PrivadoVPN).
Let’s look at some of the available protocols and see how they stack up against one another.
PPTP
Point-to-point tunneling is one of the pioneering solutions developed by Microsoft in the early days of the Internet. Integrated with Windows 95, this was (at the time) a revolutionary addition for everyday users. PPTP is the granddaddy of VPN protocols.
While PPTP is the fastest protocol on this list, it is also the least secure. Hackers and governments have long been able to decrypt the security algorithms it provides. It’s not uncommon for bad actors to take advantage of the lack of security to monitor PPTP traffic.
We obviously highly discourage you from relying on this protocol but want to give it props for starting the process that brought us here.

OpenVPN
Even though OpenVPN was released in 2001, it is still considered one of the most reliable protocols on our list. The technology has aged well because it has a passionate community of developers that work on open-source code. OpenVPN is highly configurable and compatible with most devices. making it the most popular client-facing protocol for general use.
While it doesn’t come built-in to your devices, is easy to set up and most VPN providers (including us) offer OpenVPN as a selection for their clients. It takes seconds to set up this protocol in the PrivadoVPN app.
In terms of speed, OpenVPN is highly variable. Because of the nature of the security provided, it tends to be slower than other protocols, but also safer. And, to be entirely honest, you’re unlikely to notice the difference in speed in most cases. Either way, take the time to find a balance between speed and security that best fits your routine.
L2TP/IPSec
L2TP stands for Layer 2 Tunnel Protocol and was born from a collaboration between Cisco and Microsoft. It’s a tunneling method, but it doesn’t actually offer a security protocol natively, which is why it’s usually paired with IPSec.
While L2TP/IPSec has no known widespread security vulnerabilities (at the time of this writing), they are proprietary technology. Furthermore, IPSec is also known for being compromised by the NSA, leaving many to abandon this tag team.
The one advantage is that L2TP/IPSec is pre-installed on most devices. The protocol defaults to UDP port 500, which makes it easy to spot traffic. Speed-wise, it stands mid-range to the rest of the protocols listed.
SSTP
Secure Socket Tunneling Protocol is another VPN protocol by Microsoft and developed for Windows Vista. Nowadays, it is integrated with most Windows products.
For our Mac lovers, this is obviously not the protocol for you. However, it is possible to get Mac SSTP compatibility support via third-party clients, though we can’t imagine why you would.
As a default service for Windows, SSTP uses AES encryption, rendering it relatively secure. Even though it is proprietary, many will consider this secure enough for their everyday activity.

IKEv2/IPSec
IKEv2 stands for Internet Key Exchange version 2. It is yet another product created by the Microsoft/Cisco collaboration following L2TP. Like its predecessor, IKEv2 is only a tunneling protocol and does not provide any encryption by itself. That is why it is also usually paired with IPSec for security and authentication purposes.
IKEv2 offers high stability and automatic re-connection capabilities. This makes it a popular solution for mobile devices where momentary connection losses are common. Further, it tends to offer security very close to OpenVPN while still being fast enough for downloading video, audio, and games.
Even though this is a proprietary solution, there are also open-source versions of it that, among other things, patch the issue that allowed back door access in the past.
What VPN Protocols to Use
VPN technologies are always changing, and there are a lot of choices you can make to customize your connection. Ultimately, that choice exists because it allows users to find the right balance of speed and security for them.
Regardless of the protocol you choose, we want to leave you with the following advice: pick a stable, open-source option that stays up-to-date with the latest security protocols.
Download PrivadoVPN
Protect your privacy with a world-class VPN. Sign up for premium access to PrivadoVPN and get unlimited monthly data, access to 300+ servers from around the world, and up to 10 simultaneous connections. Get a top-rated VPN that can secure your privacy at home, at work, or on the go.
Sign up for PrivadoVPN today!